Vulnerable plugins and themes are the #1 reason WordPress websites get hacked. The weekly WordPress Vulnerability Report powered by WPScan covers recent WordPress plugin, theme, and core vulnerabilities, and what to do if you run one of the vulnerable plugins or themes on your website.
Each vulnerability will have a severity rating of Low, Medium, High, or Critical. Responsible disclosure and reporting of vulnerabilities is an integral part of keeping the WordPress community safe.
Please share this post with your friends to help get the word out and make WordPress safer for everyone.
Contents of the December 8, 2021 Report
Want this report delivered to your inbox each week?
WordPress News: Gravatar Data Leak
This week Gravatar, a global service for unique avatars, was breached – although Gravatar assures there was no hack.
Hello everyone, we would like to confirm Gravatar was not hacked and no security protocols have been breached – for more information please visit: https://t.co/hhIQQ5WWKt
— Gravatar.com (@gravatar) December 7, 2021
The data was scraped, which is not a breach because passwords and other private information weren’t taken. Instead, publicly available information was gathered in a way that is not normally easy to obtain. Theoretically, someone would have to know the username of the Gravatar user in order to access the email address of that user. The scraping allowed the attacker to download the usernames and the emails at the same time.
WordPress Core Vulnerabilities
The latest version of WordPress core is 5.8.2. As a best practice, always be sure to run the latest version of WordPress core!
WordPress Plugin Vulnerabilities
In this section, the latest WordPress plugin vulnerabilities have been disclosed. Each plugin listing includes the type of vulnerability, the version number if patched, and the severity rating.
1. Events Manager
Plugin: Events Manager
Vulnerability: Admin+ SQL Injection
Patched in Version: 5.9.8
Severity Score: Medium
The vulnerability is patched, so you should update to version 5.9.8.
Plugin: Events Manager
Vulnerability: Cross-Site Scripting (XSS)
Patched in Version: 5.9.8
Severity Score: Low
The vulnerability is patched, so you should update to version 5.9.8.
2. Rich Reviews by Starfish

Plugin: Rich Reviews by Starfish
Vulnerability: Admin+ SQL Injection
Patched in Version: 1.9.6
Severity Score: Medium
The vulnerability is patched, so you should update to version 1.9.6.
3. Typebot
Plugin: Typebot
Vulnerability: Admin+ Stored Cross Site Scripting
Patched in Version: 1.4.3
Severity Score: Low
The vulnerability is patched, so you should update to version 1.4.3.
4. Contact Form & Lead Form Elementor Builder

Plugin: Contact Form & Lead Form Elementor Builder
Vulnerability: Unauthenticated Stored Cross-Site Scripting
Patched in Version: 1.6.4
Severity Score: High
The vulnerability is patched, so you should update to version 1.6.4.
5. Download Manager

Plugin: Download Manager
Vulnerability: Subscriber+ Stored Cross-Site Scripting
Patched in Version: 3.2.22
Severity Score: High
The vulnerability is patched, so you should update to version 3.2.22.
6. WP RSS Aggregator
Plugin: Subscriber+ Stored Cross-Site Scripting
Vulnerability: Admin+ SQL Injection
Patched in Version: 4.19.3
Severity Score: High
The vulnerability is patched, so you should update to version 4.19.3.
7. Buttonizer – Smart Floating Action Button

Plugin: Buttonizer – Smart Floating Action Button
Vulnerability: Admin+ Stored Cross-Site Scripting
Patched in Version: 2.5.5
Severity Score: Low
The vulnerability is patched, so you should update to version 2.5.5.
8. WP Mail Logging

Plugin: WP Mail Logging
Vulnerability: Outdated Redux Framework
Patched in Version: 1.10.0
Severity Score: Medium
The vulnerability is patched, so you should update to version 1.10.0.
9. Stetic
Plugin: Stetic
Vulnerability: CSRF to Stored Cross-Site Scripting
Patched in Version: No known fix – plugin closed
Severity Score: High
This vulnerability has NOT been patched. This plugin has been closed as of Novermber 20, 2021. Uninstall and delete.
10. Contact Form With Captcha
Plugin: Contact Form With Captcha
Vulnerability: CSRF to Stored Cross-Site Scripting
Patched in Version: No known fix – plugin closed
Severity Score: High
This vulnerability has NOT been patched. This plugin has been closed as of Novermber 26, 2021. Uninstall and delete.
11. Awesome Support

Plugin: Awesome Support
Vulnerability: Reflected Cross-Site Scripting
Patched in Version: 6.0.7
Severity Score: High
The vulnerability is patched, so you should update to version 6.0.7.
12. Asgaros Forums

Plugin: Asgaros Forums
Vulnerability: Admin+ Stored Cross-Site Scripting
Patched in Version: 1.15.14
Severity Score: Low
The vulnerability is patched, so you should update to version 1.15.14.
13. LiteSpeed Cache

Plugin: LiteSpeed Cache
Vulnerability: IP Check Bypass to Unauthenticated Stored XSS
Patched in Version: 4.4.4
Severity Score: High
The vulnerability is patched, so you should update to version 4.4.4.
Plugin: LiteSpeed Cache
Vulnerability: Admin+ Reflected Cross-Site Scripting
Patched in Version: 4.4.4
Severity Score: High
The vulnerability is patched, so you should update to version 4.4.4.
14. Video Conferencing with Zoom

Plugin: Video Conferencing with Zoom
Vulnerability: Reflected Cross-Site Scripting
Patched in Version: 3.8.16
Severity Score: High
The vulnerability is patched, so you should update to version 3.8.16.
15. Booster for Woocommerce

Plugin: Booster for Woocommerce
Vulnerability: Reflected Cross-Site Scripting in PDF Invoicing Module
Patched in Version: 5.4.9
Severity Score: High
The vulnerability is patched, so you should update to version 5.4.9.
Plugin: Booster for Woocommerce
Vulnerability: Reflected Cross-Site Scripting in General Module
Patched in Version: 5.4.9
Severity Score: High
The vulnerability is patched, so you should update to version 5.4.9.
Plugin: Booster for Woocommerce
Vulnerability: Reflected Cross-Site Scripting in Product XML Feeds Module
Patched in Version: 5.4.9
Severity Score: High
The vulnerability is patched, so you should update to version 5.4.9.
16. Speed Booster Pack

Plugin: Speed Booster Pack
Vulnerability: Admin+ SQL Injection
Patched in Version: 4.3.3.1
Severity Score: Medium
The vulnerability is patched, so you should update to version 4.3.3.1.
17. OMGF
Plugin: OMGF
Vulnerability: Admin+ Arbitrary Folder Deletion via Path Traversal
Patched in Version: 4.5.12
Severity Score: Medium
The vulnerability is patched, so you should update to version 4.5.12.
18. CAOS
Plugin: CAOS
Vulnerability: Admin+ Arbitrary Folder Deletion via Path Traversal
Patched in Version: 4.1.9
Severity Score: Medium
The vulnerability is patched, so you should update to version 4.1.9.
19. WP Travel Engine
Plugin: WP Travel Engine
Vulnerability: Editor+ Stored Cross-Site Scripting
Patched in Version: 5.3.1
Severity Score: Low
The vulnerability is patched, so you should update to version 5.3.1.
20. Download Monitor

Plugin: Download Monitor
Vulnerability: Admin+ SQL Injection
Patched in Version: 4.4.5
Severity Score: Medium
The vulnerability is patched, so you should update to version 4.4.5.
21. Mortgage Calculator / Loan Calculator
Plugin: Mortgage Calculator / Loan Calculator
Vulnerability: Contributor+ Stored Cross-Site Scripting
Patched in Version: 1.5.17
Severity Score: Medium
The vulnerability is patched, so you should update to version 1.5.17.
22. Variation Swatches for WooCommerce
Plugin: Variation Swatches for WooCommerce
Vulnerability: Subscriber+ Stored Cross-Site Scripting
Patched in Version: 2.1.2
Severity Score: High
The vulnerability is patched, so you should update to version 2.1.2.
23. ClickBank Affiliate Ads
Plugin: ClickBank Affiliate Ads
Vulnerability: CSRF to Stored Cross-Site Scripting
Patched in Version: No known fix – plugin closed
Severity Score: High
This vulnerability has NOT been patched. This plugin has been closed as of December 1, 2021. Uninstall and delete.
Plugin: ClickBank Affiliate Ads
Vulnerability: Admin+ Stored Cross-Site Scripting
Patched in Version: No known fix – plugin closed
Severity Score: Low
This vulnerability has NOT been patched. This plugin has been closed as of December 1, 2021. Uninstall and delete.
24. Advanced Custom Fields
Plugin: Advanced Custom Fields
Vulnerability: Subscriber+ Arbitrary ACF Data/Field Groups View and Fields Move
Patched in Version: 5.11
Severity Score: Medium
The vulnerability is patched, so you should update to version 5.11.
25. Canto

Plugin: Canto
Vulnerability: Unauthenticated Blind SSRF
Patched in Version: No known fix
Severity Score: Medium
This vulnerability has NOT been patched. Uninstall and delete the plugin until a patch is released.
26. All-In-One-Gallery

Plugin: All-In-One-Gallery
Vulnerability: Admin+ Local File Inclusion
Patched in Version: 2.5.0
Severity Score: Low
The vulnerability is patched, so you should update to version 2.5.0.
How to Protect Your WordPress Website From Vulnerable Plugins and Themes
As you can see from this report, lots of new WordPress plugin and theme vulnerabilities are disclosed each week. We know it can be difficult to stay on top of every reported vulnerability disclosure, so the iThemes Security Pro plugin makes it easy to make sure your site isn’t running a theme, plugin, or WordPress core version with a known vulnerability.
Get iThemes Security Pro with 24/7 Website Security Monitoring
iThemes Security Pro, our WordPress security plugin, offers 50+ ways to secure and protect your website from common WordPress security vulnerabilities. With WordPress, two-factor authentication, brute force protection, strong password enforcement, and more, you can add extra layers of security to your website.
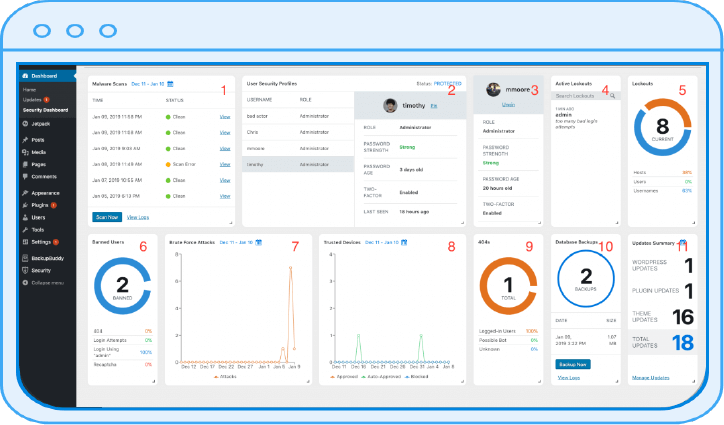
Get iThemes Security Pro
![]()
Each week, Michael puts together the WordPress Vulnerability Report to help keep your sites safe. As Product Manager at iThemes, he helps us continue to improve the iThemes product lineup. He’s a giant nerd & loves learning about all things tech, old & new. You can find Michael hanging out with his wife & daughter, reading or listening to music when not working.

Keep reading the article at WordPress News and Updates from iThemes – iThemes. The article was originally written by Michael Moore on 2021-12-08 12:49:55.
The article was hand-picked and curated for you by the Editorial Team of WP Archives.