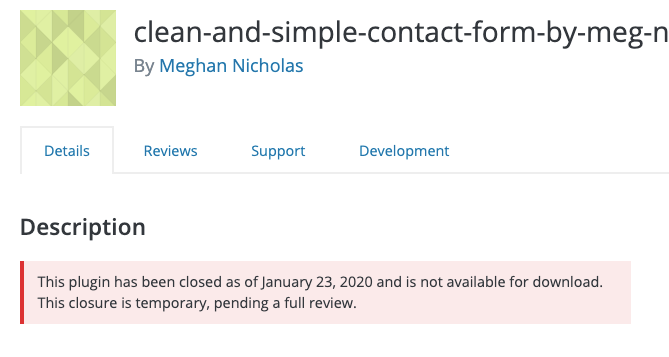
Remove Scountet Kalendar as it appears the plugin has been abandoned.
The vulnerability has been patched, and you should update it to version 1.6.90.
2. Materialis
Materialis versions 1.0.172 and below have an Authenticated Options Update vulnerability.
What You Should Do
The vulnerability has been patched, and you should update it to version 1.0.173.
4. Superlist
Superlist versions 2.9.2 and below are vulnerable to a Stored Cross-Site Scripting attack.
What You Should Do
The vulnerability hasn’t been patched, and you should remove the theme. Keep an eye on the changelog for a security update.
How to Be Proactive About WordPress Theme & Plugin Vulnerabilities
Running outdated software is the number one reason WordPress sites are hacked. It is crucial to the security of your WordPress site that you have an update routine. You should be logging into your sites at least once a week to perform updates.
Automatic Updates Can Help
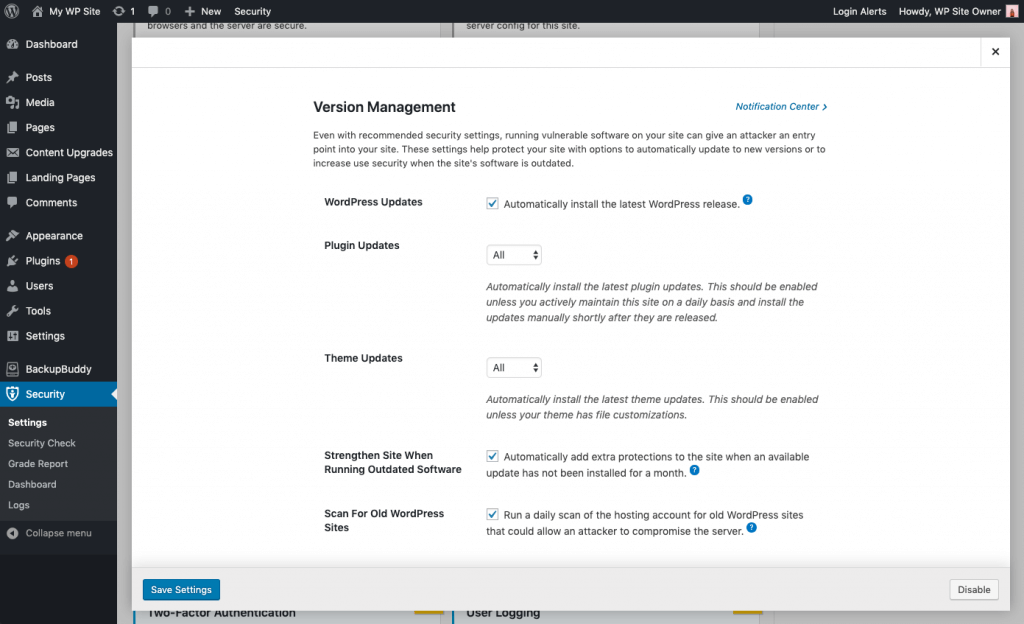
Automatic updates are a great choice for WordPress websites that don’t change very often. Lack of attention often leaves these sites neglected and vulnerable to attacks. Even with recommended security settings, running vulnerable software on your site can give an attacker an entry point into your site.
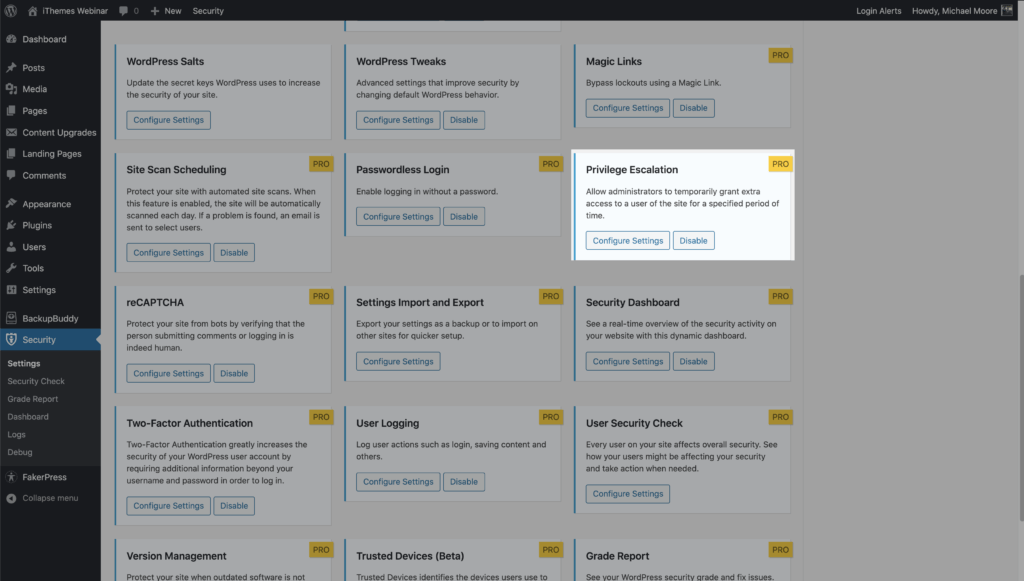
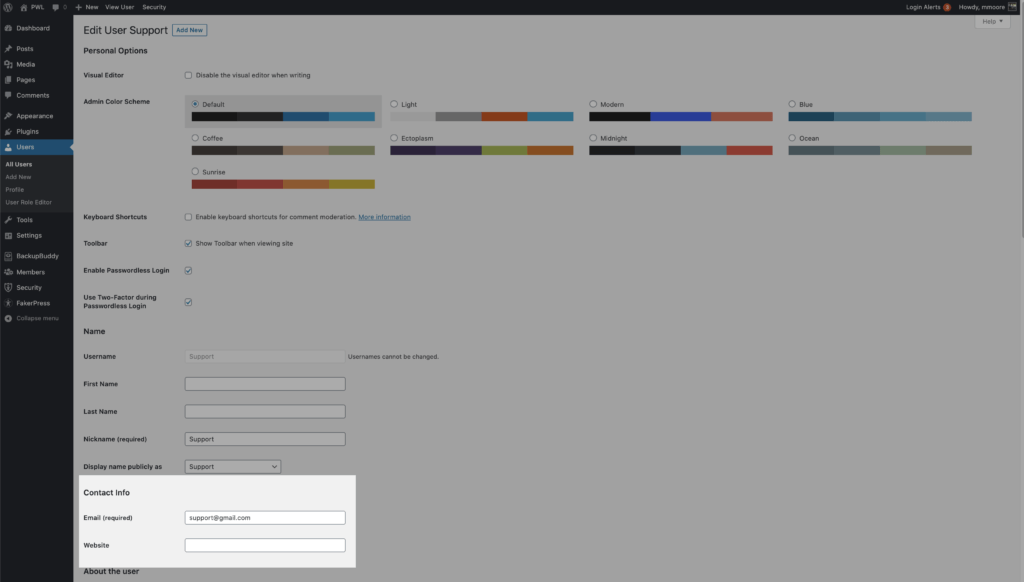
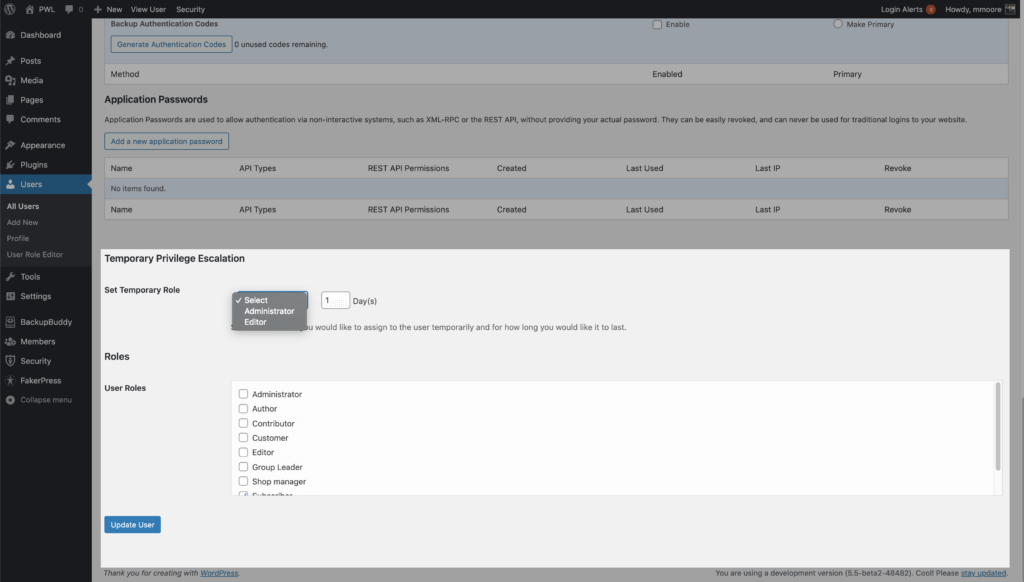
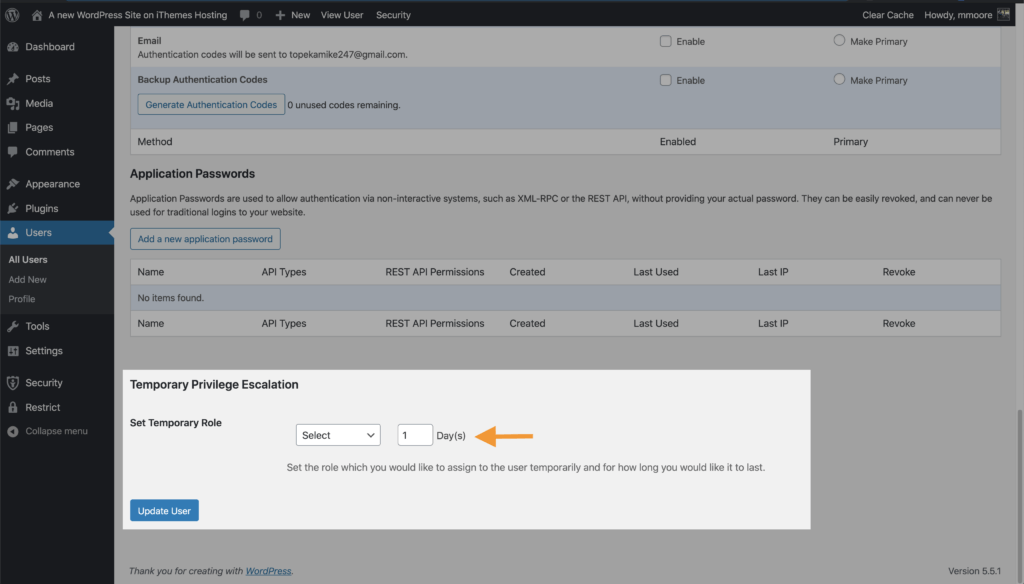
Using the iThemes Security Pro plugin’s Version Management feature, you can enable automatic WordPress updates to ensure you are getting the latest security patches. These settings help protect your site with options to automatically update to new versions or to increase user security when the site’s software is outdated.
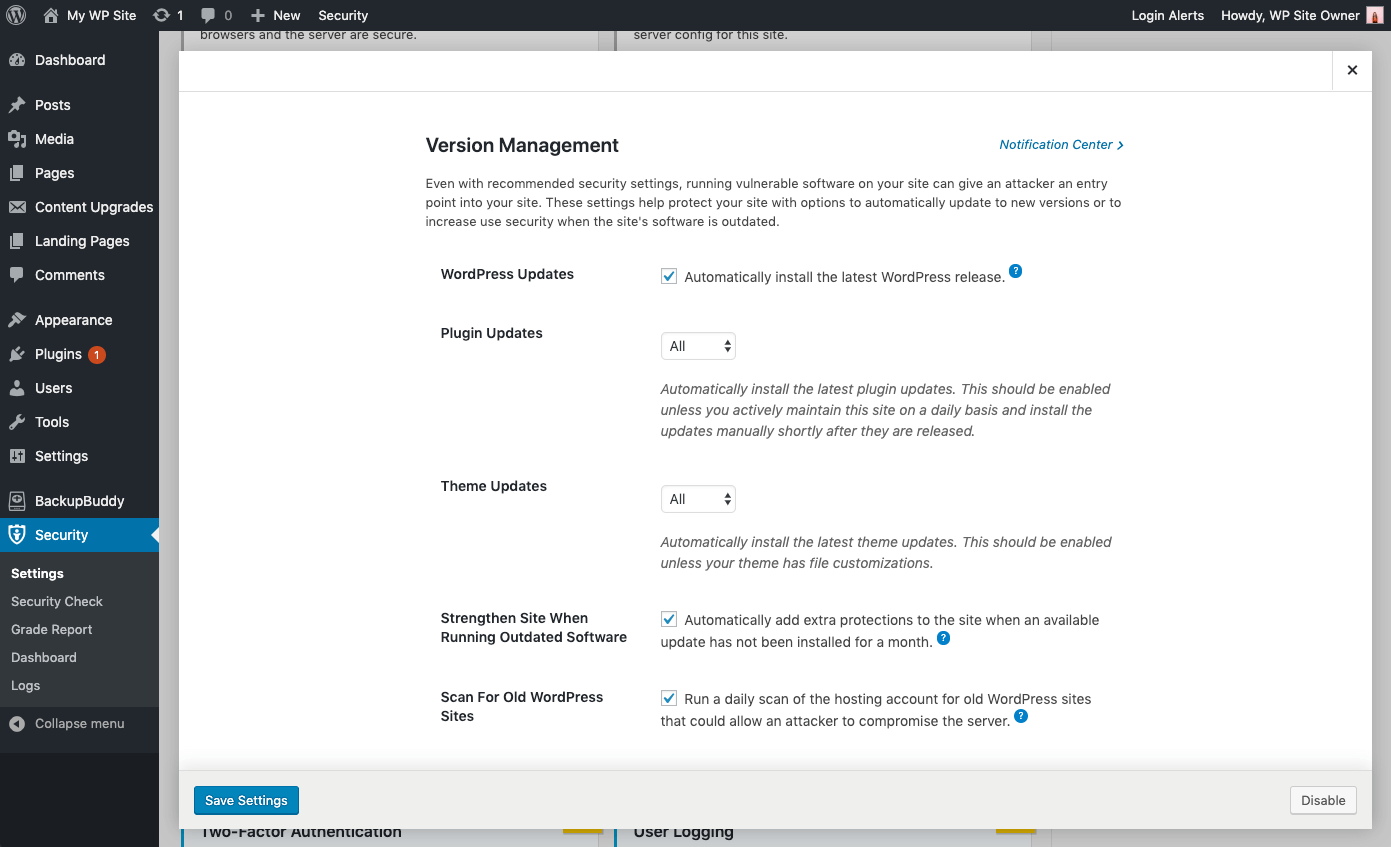
Version Management Update Options
- WordPress Updates –Automatically install the latest WordPress release.
- Plugin Automatic Updates – Automatically install the latest plugin updates. This should be enabled unless you actively maintain this site on a daily basis and install the updates manually shortly after they are released.
- Theme Automatic Updates – Automatically install the latest theme updates. This should be enabled unless your theme has file customizations.
- Granular Control over Plugin and Theme updates – You may have plugins/themes that you’d like to either manually update, or delay the update until the release has had time to prove stable. You can choose Custom for the opportunity to assign each plugin or theme to either update immediately (Enable), not update automatically at all (Disable) or update with a delay of a specified amount of days (Delay).
Strengthening and Alerting to Critical Issues
- Strengthen Site When Running Outdated Software – Automatically add extra protections to the site when an available update has not been installed for a month. The iThemes Security plugin will automatically enable stricter security when an update has not been installed for a month. First, it will force all users that do not have two-factor enabled to provide a login code sent to their email address before logging back in. Second, it will disable the WP File Editor (to block people from editing plugin or theme code), XML-RPC pingbacks, and block multiple authentication attempts per XML-RPC request (both of which will make XML-RPC stronger against attacks without having to turn it off completely).
- Scan for Other Old WordPress Sites – This will checks for other outdated WordPress installs on your hosting account. A single outdated WordPress site with a vulnerability could allow attackers to compromise all the other sites on the same hosting account.
- Send Email Notifications – For issues that require intervention, an email is sent to admin-level users.
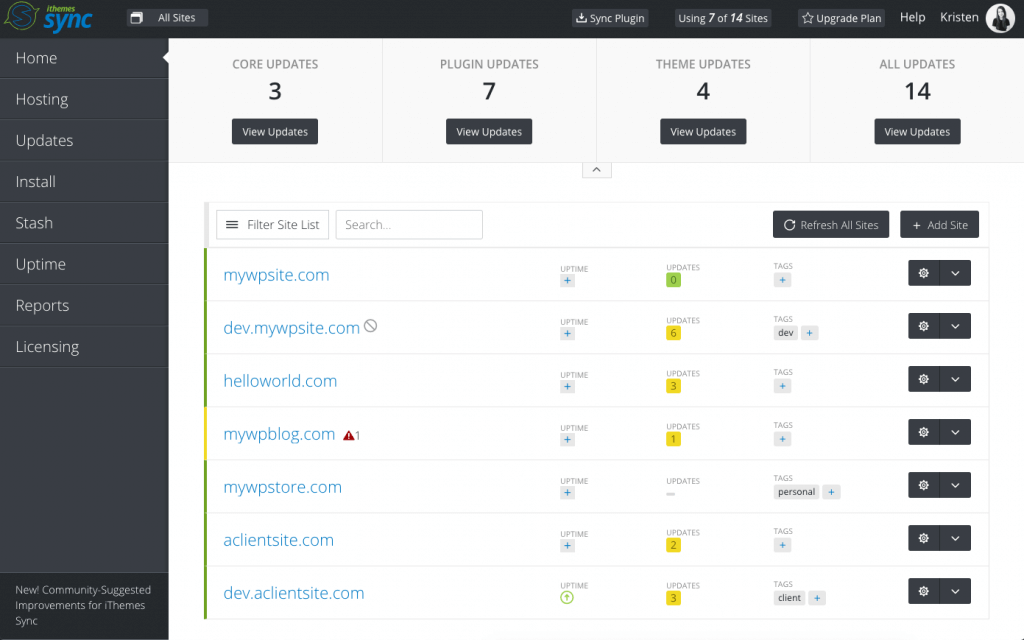
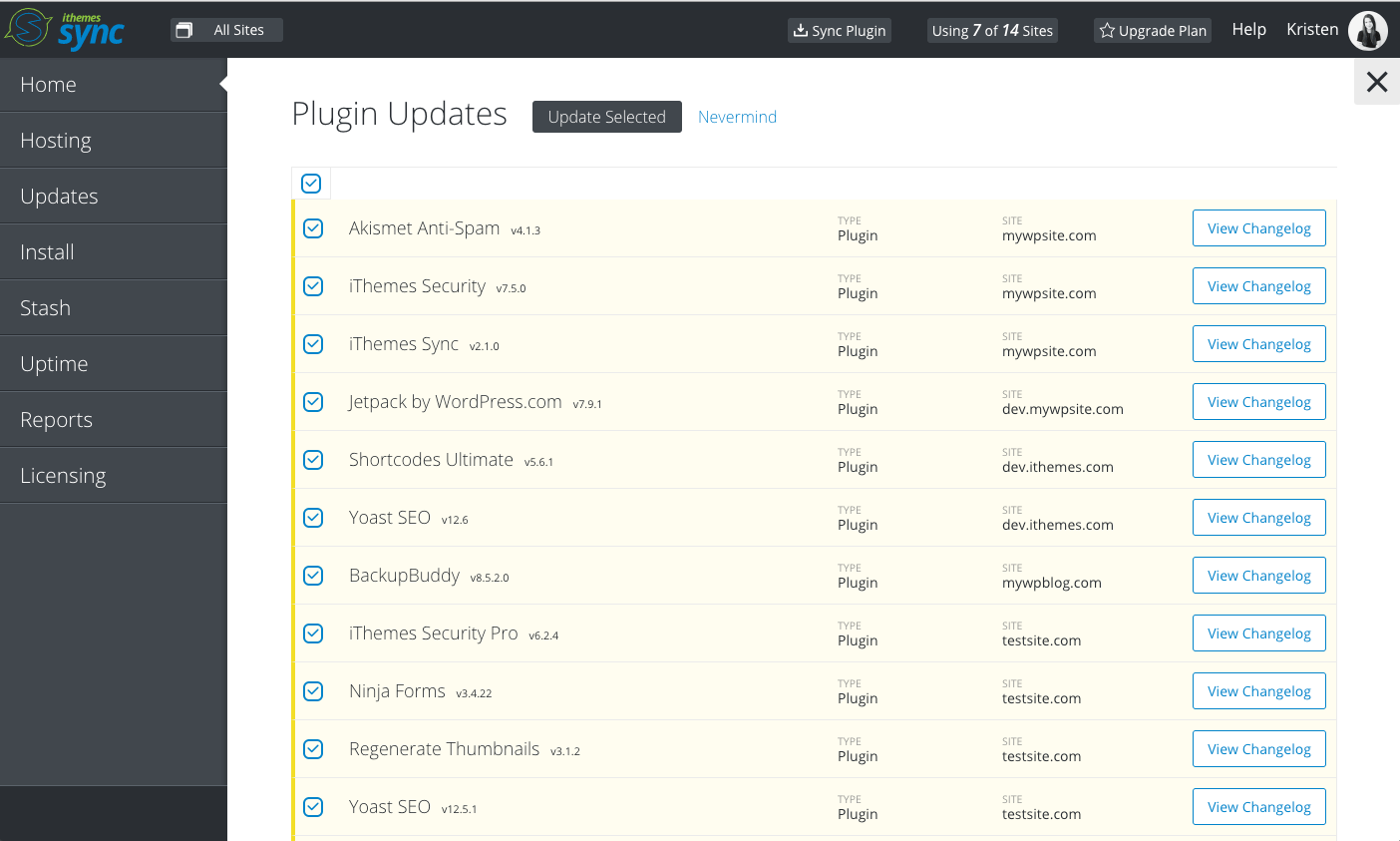
Managing Multiple WP Sites? Update Plugins, Themes & Core At Once from the iThemes Sync Dashboard
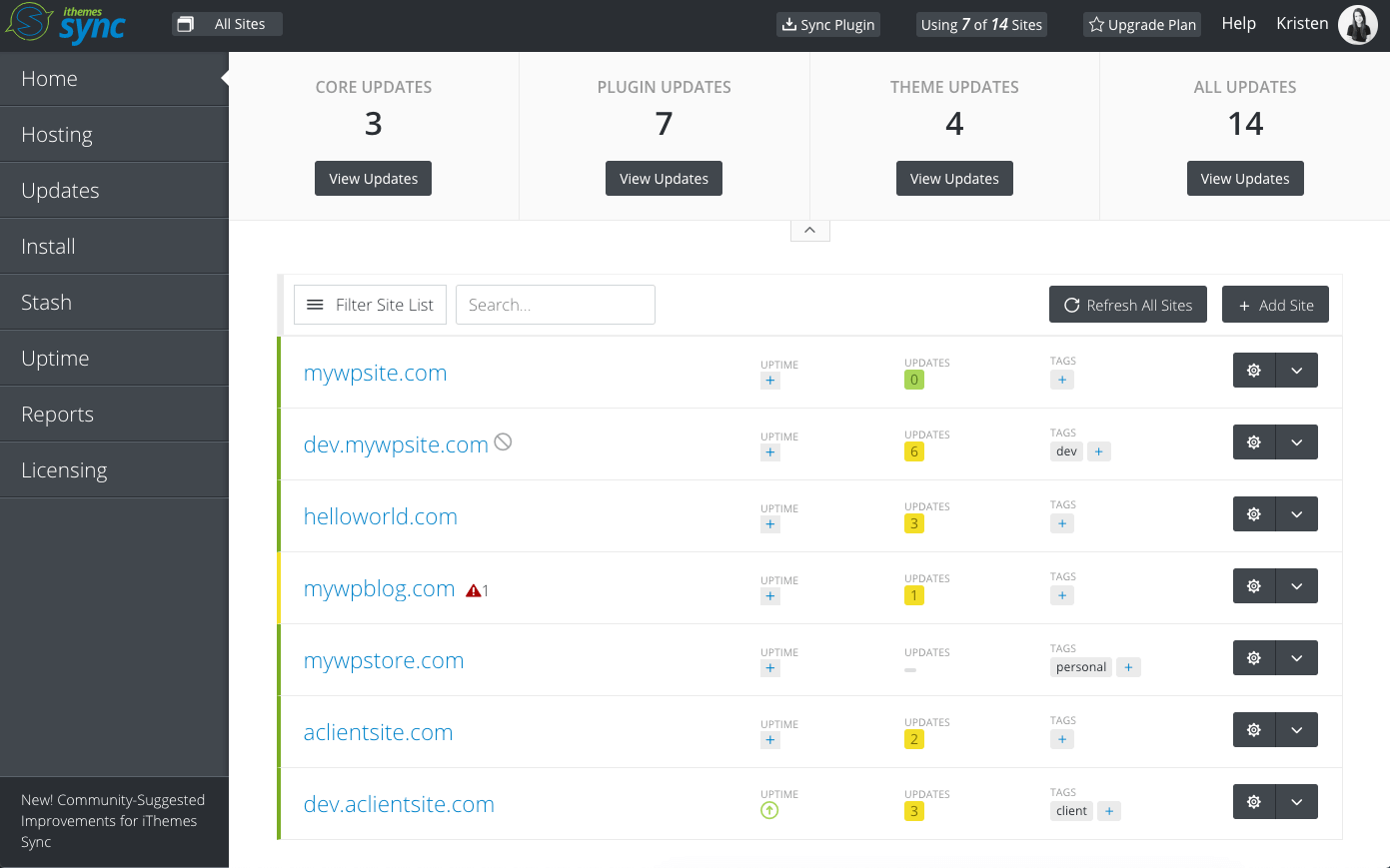
iThemes Sync is our central dashboard to help you manage multiple WordPress sites. From the Sync dashboard, you can view available updates for all your sites and then update plugins, themes, and WordPress core with one click. You can also get daily email notifications when a new version update is available.
Breaches From Around the Web
We include breaches from around the web because it is essential to also be aware of vulnerabilities outside of the WordPress ecosystem. Exploits to server software can expose sensitive data. Database breaches can expose the credentials for the users on your site, opening the door for attackers to access your site.
1. Ring Camera Hacks

Unfortunately, some families are reporting episodes of harassment after their Ring devices were hacked. If you are using any security camera that allows you to remotely view a live feed, you should know how hackers are breaking into Ring Cameras.
According to a Ring spokesperson, these reports of hacks were isolated and weren’t related to hacked or breached of Ring Security. That is excellent news, and it means the likely culprit of the hacks were weak passwords and not using 2FA. A brute force attack, when a malicious bot tries a random combination of usernames and passwords until one is successful, and they can gain access to your account.
Luckily for us, it is pretty easy to protect your accounts from a brute force attack. According to Google security researches say that using two-factor authentication will stop 100% of bot attacks If you are installing an IoT device–especially one that allows you to see and hear what is happening inside your house–make sure you protect you and your family by using a strong password and two-factor authentication.
Summary of WordPress Vulnerabilities for
December 2019, Part 1
Core
These vulnerabilities have been patched, and you should update it to version 5.3.1.
Plugins
The vulnerability has been patched, and you should update it to version 7.1.10.
The vulnerability has been patched, and you should update it to version 1.24.1.
The vulnerability has been patched, and you should update it to version 1.20.1.
The vulnerability has been patched, and you should update it to version 4.07.
You should remove the Scountet Kalendar. It appears the plugin has been abandoned and is no longer being maintained.
The vulnerability has been patched, and you should update it to version 1.4.
Themes
The vulnerability has been patched, and you should update it to version 1.6.90.
The vulnerability has been patched, and you should update it to version 1.0.173.
The vulnerability has been patched, and you should update it to version 2.0.14.5.
The vulnerability has been patched, and you should update it to version 1.0.173.
A WordPress Security Plugin Can Help Secure Your Website
iThemes Security Pro, our WordPress security plugin, offers 30+ ways to secure and protect your website from common WordPress security vulnerabilities. With WordPress, two-factor authentication, brute force protection, strong password enforcement, and more, you can add an extra layer of security to your website.
Get iThemes Security
Keep reading the article at WordPress News and Updates from iThemes – iThemes. The article was originally written by Michael Moore on 2019-12-13 10:37:58.
The article was hand-picked and curated for you by the Editorial Team of WP Archives.